What is Action Message Format (AMF) ? TL;DR;
AMF is a binary message serialization format geared for remote procedure calls, native to the Adobe Flash Player and Adobe Integrated Runtime. There are two versions of the format, AMF0 and AMF3. AMF3 is more compact than AMF0, and and supports data types that are available only in ActionScript 3.0, such as ByteArray.
Tools Required :
1. Burpsuite < Download >
2. amf-deserializer Burpsuite Extender Plugin < Download >
3. Blazer Burpsuite Extender Plugin < Download >
Testing Approach :
Step 1. Intercept AMF request or procedure calls using burpsuite.
Step 2. Decode AMF objects using amf-deserializer.
Step 3. Create new requests via converting AMF request to XML using amf-deserializer.
Step 4. Once the request is created import XML requests in burp suite repeater.
Step 5. Now, once you see all XML parameters via clicking on XML tab. One can use those parameters as entry/injection points for further web application attacks(SQL, LFI, XSS etc. manual tests)
Step 6. Automate security tests using Burpsuite scanner or Blazer extender for burpsuite.
A Penetration Testing #TrueStory - XML External Entity (XXE) Bugs to rescue :
Recently me and my team was requested to perform external and internal security audit for an organization. The organization which we were going to test was very updated in cyber security field. They have a process of doing 360 security audits quarterly with various precaution taken like IDS, WAF, FW and Honeypots installed for there networks and applications. Our team was assigned task to perform external as-well-as internal penetration testing of there netwoks and applications. As my expertise is more in Application Security I took apps testing part where as network assessment part wask taken by my team.
After four weeks of assessment, we started sharing our finding to client. Nework assessment was going great as team was able to find out many unpatched and outdated systems, softwares, packages in network. On other hand application security assessment was not going good as planned because I was unable to find any Critical or High severity vulnerabilities.
Deadline was near to submit final report so I started working on a report. While working on a report I opened my burpsuite session for one of the application to calculate number of links, parameters etc... and suddenly I relaised I have made a biggest mistake...!
The mistake was, I forgot to filter out "Flash files" & "Other Binary". On checking the checkbox I found various filetype like SVG, AFM, ZIP etc. added to my burp session.
After analysing updated files in my session, I sorted out AFM flash application files and quickly downloaded and installed the "amf-deserializer Burpsuite Extender Plugin" in my brupsuite to decode the AMF file content and extract some juicy informations.
Once the plugin is loaded succesfully you will see the "Deserialized AMF" tab in whick you can see the AMF object decoded in XML format.
Now, I converted all AMF objects to XML requests and started my security tests using burpsuite and Blazer.
A. AMF Request
B. Deserialized AMF
1. Download Blazer
3. For automating the tests using blazer - right click on AMF request and click on "Blazer - AMF testing" option.
As I was having less time to test this application I used burp scanner to automate security tests for converted AMF requests.
After an hour of automation I got alerts for XXE Injection. For exploiting XXE injection I used converted AMF request's XML parameters and created a new XML request in repeater.
Steps to Reproduce XXE Exploitation :
1. Send vulnerable AFM request to repeater.
2. Navigate to Deserialized AMF tab and in XML content set XXE payload in XML parameters(Entry points/Injection Points)
3. Then, re-play the request.
And finally my assessment was finished as I found more critical and high severity vulnerabilities like SQLi, XSS & OTP bruteforce in application via manupluating converted AMF request's XML's parameters.
AMF is a binary message serialization format geared for remote procedure calls, native to the Adobe Flash Player and Adobe Integrated Runtime. There are two versions of the format, AMF0 and AMF3. AMF3 is more compact than AMF0, and and supports data types that are available only in ActionScript 3.0, such as ByteArray.
Tools Required :
1. Burpsuite < Download >
2. amf-deserializer Burpsuite Extender Plugin < Download >
3. Blazer Burpsuite Extender Plugin < Download >
Testing Approach :
Step 1. Intercept AMF request or procedure calls using burpsuite.
Step 2. Decode AMF objects using amf-deserializer.
Step 3. Create new requests via converting AMF request to XML using amf-deserializer.
Step 4. Once the request is created import XML requests in burp suite repeater.
Step 5. Now, once you see all XML parameters via clicking on XML tab. One can use those parameters as entry/injection points for further web application attacks(SQL, LFI, XSS etc. manual tests)
Step 6. Automate security tests using Burpsuite scanner or Blazer extender for burpsuite.
A Penetration Testing #TrueStory - XML External Entity (XXE) Bugs to rescue :
Recently me and my team was requested to perform external and internal security audit for an organization. The organization which we were going to test was very updated in cyber security field. They have a process of doing 360 security audits quarterly with various precaution taken like IDS, WAF, FW and Honeypots installed for there networks and applications. Our team was assigned task to perform external as-well-as internal penetration testing of there netwoks and applications. As my expertise is more in Application Security I took apps testing part where as network assessment part wask taken by my team.
After four weeks of assessment, we started sharing our finding to client. Nework assessment was going great as team was able to find out many unpatched and outdated systems, softwares, packages in network. On other hand application security assessment was not going good as planned because I was unable to find any Critical or High severity vulnerabilities.
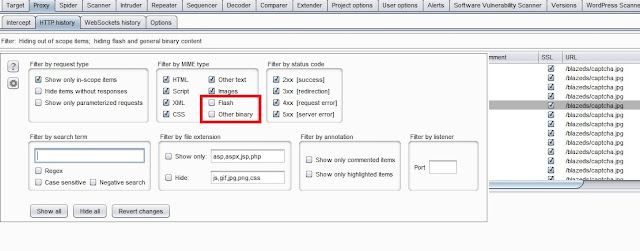
Deadline was near to submit final report so I started working on a report. While working on a report I opened my burpsuite session for one of the application to calculate number of links, parameters etc... and suddenly I relaised I have made a biggest mistake...!
Figure 1. The Mistake
Figure 2. Rectification of mistake
After analysing updated files in my session, I sorted out AFM flash application files and quickly downloaded and installed the "amf-deserializer Burpsuite Extender Plugin" in my brupsuite to decode the AMF file content and extract some juicy informations.
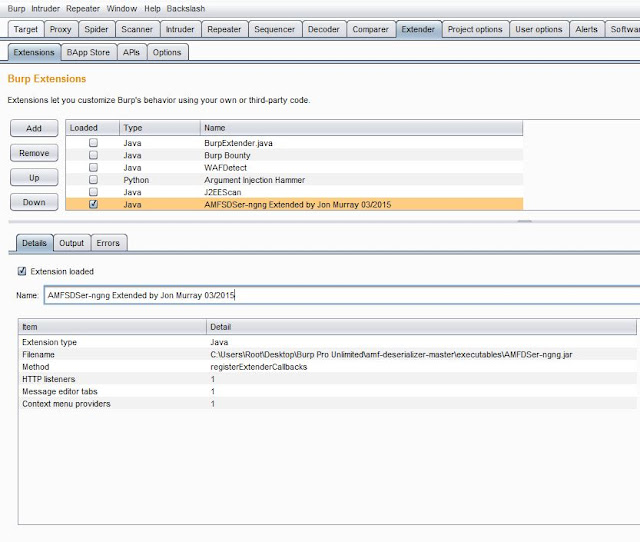
Figure 3. amf-deserializer project
1. Download the amf-deserializer project and extract it in some folder.
2. Open burpsuite
3. Navigate to Extender tab and add the java file "\amf-deserializer-master\executables\AMFDSer-ngng.jar"
Figure 4. Inporting AMFDSer-ngng.jar
4. Load the AMFD plugin
Figure 5. Loading AMFDSer-ngng.jar
Now, I converted all AMF objects to XML requests and started my security tests using burpsuite and Blazer.
A. AMF Request
Figure a. AMF Request
Figure b. Deserialized AMF
Figure 6. Blazer project
2. Navigate to Extender tab then BApps Store and Import Blazer.
Figure 7. Loading Blazer
3. For automating the tests using blazer - right click on AMF request and click on "Blazer - AMF testing" option.
Figure 8. Automating test using Blazer
As I was having less time to test this application I used burp scanner to automate security tests for converted AMF requests.
Figure 9. Burpsuite scanner result
After an hour of automation I got alerts for XXE Injection. For exploiting XXE injection I used converted AMF request's XML parameters and created a new XML request in repeater.
Steps to Reproduce XXE Exploitation :
1. Send vulnerable AFM request to repeater.
2. Navigate to Deserialized AMF tab and in XML content set XXE payload in XML parameters(Entry points/Injection Points)
3. Then, re-play the request.
Figure 10. Creating vulnerable request
Figure 11. Vulnerable request response
And finally my assessment was finished as I found more critical and high severity vulnerabilities like SQLi, XSS & OTP bruteforce in application via manupluating converted AMF request's XML's parameters.